[ad_1]

Hackers are actively exploiting a high-severity vulnerability within the widespread Elementor Professional WordPress plugin utilized by over eleven million web sites.
Elementor Professional is a WordPress web page builder plugin permitting customers to simply construct professional-looking websites with out figuring out tips on how to code, that includes drag and drop, theme constructing, a template assortment, customized widget assist, and a WooCommerce builder for on-line outlets.
This vulnerability was found by NinTechNet researcher Jerome Bruandet on March 18, 2023, who shared technical particulars this week about how the bug will be exploited when put in alongside WooCommerce.
The difficulty, which impacts v3.11.6 and all variations earlier than it, permits authenticated customers, like store prospects or web site members, to alter the positioning’s settings and even carry out an entire web site takeover.
The researcher defined that the flaw issues a damaged entry management on the plugin’s WooCommerce module (“elementor-pro/modules/woocommerce/module.php”), permitting anybody to switch WordPress choices within the database with out correct validation.
The flaw is exploited by a weak AJAX motion, “pro_woocommerce_update_page_option,” which suffers from poorly applied enter validation and an absence of functionality checks.
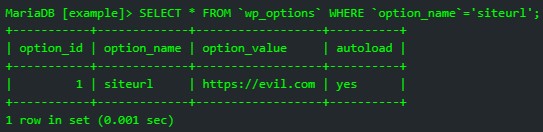
“An authenticated attacker can leverage the vulnerability to create an administrator account by enabling registration and setting the default function to “administrator,” change the administrator electronic mail handle or, redirect all visitors to an exterior malicious web site by altering siteurl amongst many different prospects,” defined Bruandet in a technical writeup in regards to the bug.
It is very important word that for the actual flaw to be exploited, the WooCommerce plugin should even be put in on the positioning, which prompts the corresponding weak module on Elementor Professional.
Elementor Plugin bug actively exploited
WordPress safety agency PatchStack is now reporting that hackers are actively exploiting this Elementor Professional plugin vulnerability to redirect guests to malicious domains (“away[.]trackersline[.]com”) or add backdoors to the breached web site.
PatchStack says the backdoor uploaded in these assaults are named wp-resortpark.zip, wp-rate.php, or lll.zip
Whereas not many particulars have been supplied relating to these backdoors, BleepingComputer discovered a pattern of the lll.zip archive, which accommodates a PHP script that enables a distant attacker to add extra recordsdata to the compromised server.
This backdoor would permit the attacker to realize full entry to the WordPress web site, whether or not to steal knowledge or set up extra malicious code.
PatchStack says many of the assaults concentrating on weak web sites originate from the next three IP addresses, so it’s instructed so as to add these to a blocklist:
- 193.169.194.63
- 193.169.195.64
- 194.135.30.6
In case your web site makes use of Elementor Professional, it’s crucial to improve to model 3.11.7 or later (the most recent accessible is 3.12.0) as quickly as doable, as hackers are already concentrating on weak web sites.
Final week, WordPress force-updated the WooCommerce Funds plugin for on-line shops to handle a essential vulnerability that allowed unauthenticated attackers to realize administrator entry to weak websites.
[ad_2]