[ad_1]

A brand new Emotet phishing marketing campaign is focusing on U.S. taxpayers by impersonating W-9 tax types allegedly despatched by the Inner Income Service and firms you’re employed with.
Emotet is a infamous malware an infection distributed via phishing emails that previously contained Microsoft Phrase and Excel paperwork with malicious macros that set up the malware.
Nonetheless, after Microsoft started blocking macros by default in downloaded Workplace paperwork, Emotet switched to utilizing Microsoft OneNote recordsdata with embedded scripts to put in the Emotet malware.
As soon as Emotet is put in, the malware will steal victims’ emails to make use of in future reply-chain assaults, ship additional spam emails, and finally set up different malware that present preliminary entry to different risk actors, similar to ransomware gangs.
Emotet gears up for the US tax season
The Emotet malware operations generally use themed phishing campaigns to coincide with holidays and yearly enterprise actions, similar to the present U.S. tax season.
In new phishing campaigns seen by safety researchers at Malwarebytes and Palo Alto Networks Unit42, the Emotet malware targets customers with emails containing faux W-9 tax type attachments.
Within the marketing campaign seen by Malwarebytes, the risk actors ship emails titled ‘IRS Tax Types W-9,’ whereas impersonating an ‘Inspector’ from the Inner Income Service.
These phishing emails comprise a ZIP archive named ‘W-9 type.zip’ that accommodates a malicious Phrase doc. This Phrase doc has been inflated to over 500MB to make it more durable for safety software program to detect it as malicious.
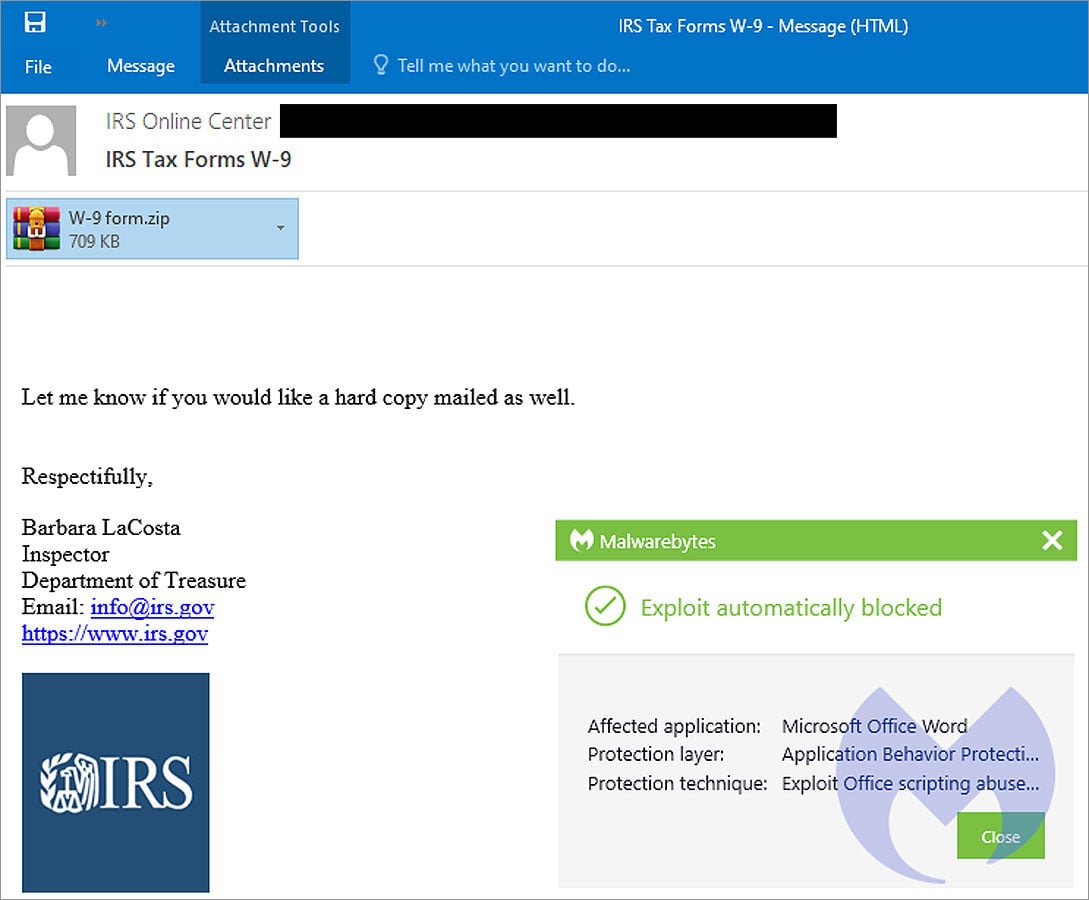
Supply: Malwarebytes
Nonetheless, now that Microsoft is obstructing macros by default, customers are much less prone to undergo the difficulty of enabling the macros and turn into contaminated utilizing malicious Phrase paperwork.
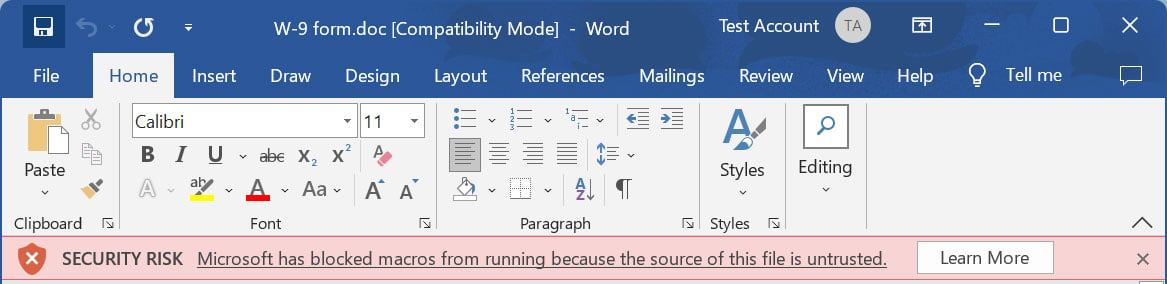
Supply: BleepingComputer
In a phishing marketing campaign seen by Brad Duncan of Unit42, the risk actors bypass these restrictions through the use of Microsoft OneNote paperwork with embedded VBScript recordsdata that set up the Emotet malware.
This phishing marketing campaign makes use of reply-chain emails containing pretending to be from enterprise companions sending you W-9 Types, as proven beneath.
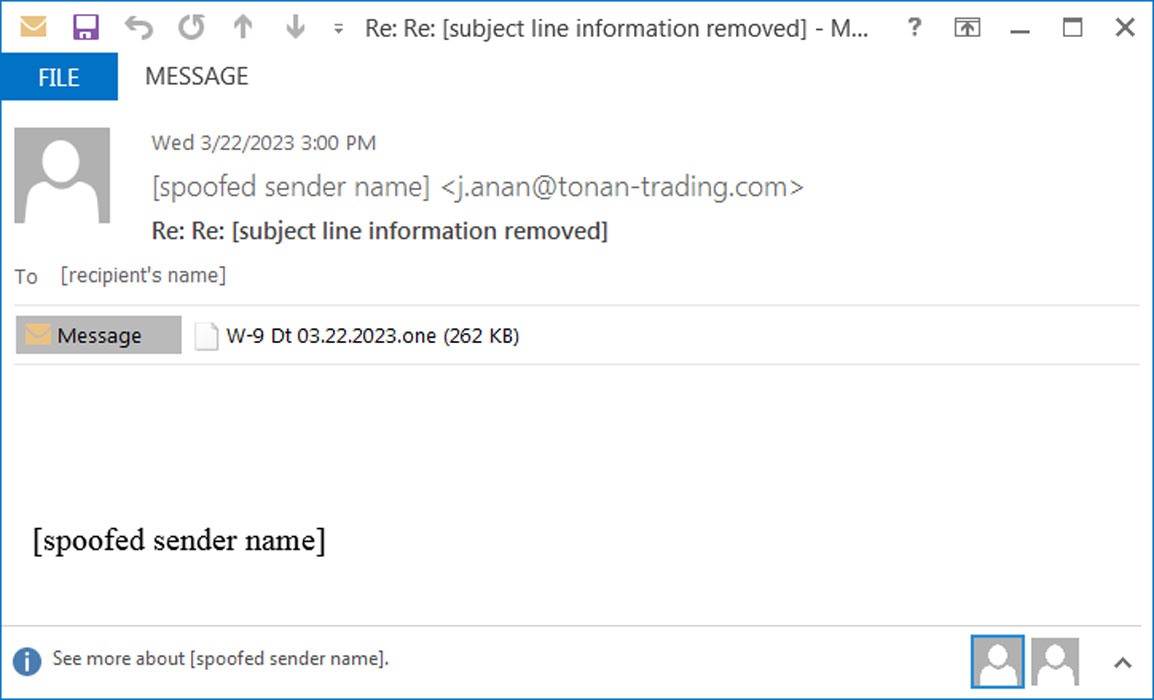
Supply: Unit42
The hooked up OneNote paperwork will fake to be protected, requesting that you just double-click the ‘View’ button to see the doc accurately. Nonetheless, hidden beneath that View button is a VBScript doc that can be launched as a substitute.
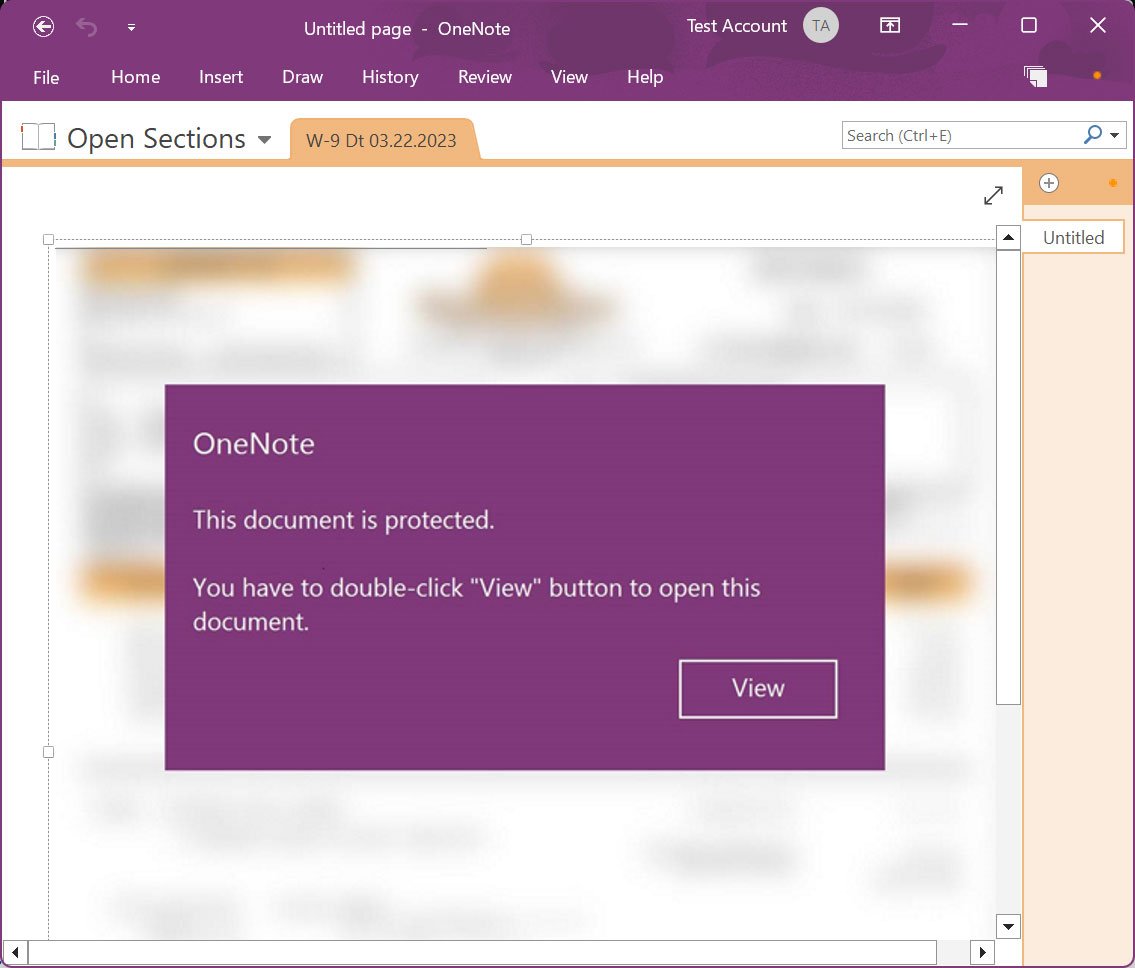
Supply: BleepingComputer
When launching the embedded VBScript file, Microsoft OneNote will warn the person that the file could also be malicious. Sadly, historical past has proven us that many customers ignore these warnings and easily permit the recordsdata to run.
As soon as executed, the VBScript will obtain the Emotet DLL and run it utilizing regsvr32.exe.
The malware will now quietly run within the background, stealing e mail, contacts, and ready for additional payloads to put in on the system.
In the event you obtain any emails claiming to be W-9 or different tax types, first scan the paperwork along with your native antivirus software program. Nonetheless, because of the delicate nature of those types, it’s not urged that you just add them to cloud-based scanning companies like VirusTotal.
Usually, tax types are distributed as PDF paperwork and never as Phrase attachments, so if you happen to obtain one, it is best to keep away from opening it and enabling macros.
Lastly, it’s uncertain that tax types would ever be despatched as OneNote paperwork, so instantly delete the e-mail and don’t open it if you happen to obtain one.
As all the time, one of the best line of protection is to discard any e mail from individuals you have no idea, and if you happen to do know them, contact them by telephone first to substantiate in the event that they despatched it.
[ad_2]